Top 5 IT & Cyber Concerns We’re Hearing from Midlands SMEs

Top 5 IT & Cyber Concerns We’re Hearing from Midlands SMEs
Over the past week, we’ve spoken with dozens of SMEs across the Midlands at local events and business conversations. While every organisation is different, the concerns coming up around IT and cyber security were strikingly consistent.
These aren’t abstract or hypothetical worries. They’re real, day‑to‑day risks that directly affect productivity, reputation, and business continuity.
Below, we break down the five most common IT and cyber concerns Midlands SMEs are raising, why they matter, and what practical steps businesses can take to reduce risk without overcomplicating things.
1 - Phishing Emails That Are Harder Than Ever to Spot
Phishing remains the number one entry point for cyber attacks — and SMEs know it.
What’s changed is how convincing these emails now look. We’re hearing concerns about:
- Emails that appear to come from trusted suppliers or internal staff
- Fake invoice requests and payment change notifications
- Messages that bypass spam filters and land directly in inboxes
For many businesses, the worry isn’t just whether a phishing email will arrive — it’s whether a member of staff will be able to spot it in time.
Why this matters:
A single click can lead to stolen credentials, compromised accounts, or even ransomware.
The practical fix:
Strong email security, multi‑factor authentication (MFA), and user awareness training dramatically reduce risk — without disrupting how teams work.
2 - Ransomware and “What If We Couldn’t Recover?”
Ransomware is no longer seen as a problem for large corporations only. Midlands SMEs are increasingly aware that they are a prime target.
The biggest concern we hear isn’t always the attack itself — it’s what happens after:
- Would we get our data back?
- How long would systems be down?
- Could we keep trading?
Many businesses have backups, but aren’t confident they are:
- Properly protected
- Regularly tested
- Separated from live systems
Why this matters:
Backups that don’t work under pressure are as risky as having no backups at all.
The practical fix:
Secure, monitored backups combined with a tested recovery plan give businesses confidence they can survive an incident, not just react to one.
3 - Ageing IT Systems Creating Hidden Risk
Legacy systems came up repeatedly in conversations with SMEs.
Common issues include:
- Devices running on unsupported operating systems
- Software that hasn’t been updated but is “too critical to change”
- Older infrastructure that no one fully understands anymore
While these systems often still work, they quietly introduce security gaps and reliability issues.
Why this matters:
Outdated systems are easier for attackers to exploit and more likely to cause unplanned downtime.
The practical fix:
You don’t need a full IT overhaul. A phased review that prioritises the highest‑risk systems first can significantly reduce exposure while keeping budgets under control.
4 - No Clear Incident Response or Cyber Plan
One of the most honest comments we heard was:
“If something serious happened… I’m not sure we’d know what to do first.”
Many SMEs don’t lack commitment to security — they lack clarity.
Questions we frequently hear:
- Who do we call if there’s a breach?
- How do we isolate affected systems?
- What do we tell customers or suppliers?
Why this matters:
In a cyber incident, confusion costs time — and time costs money.
The practical fix:
A simple incident response plan, even a short one, gives teams confidence and structure during stressful moments. It doesn’t need to be complex — it just needs to exist.
5 - Confusion Around Cyber Essentials and Compliance
Cyber Essentials came up in almost every conversation — often with uncertainty attached.
Businesses told us they weren’t sure:
- Whether Cyber Essentials applies to them
- What’s actually involved
- If it’s a “tick‑box” exercise or a real security improvement
For some, it’s driven by supply‑chain pressure or contracts. For others, it’s about demonstrating good cyber hygiene.
Why this matters:
Cyber Essentials isn’t just about certification — it’s about putting proven baseline controls in place that block the most common attacks.
The practical fix:
With the right guidance, Cyber Essentials becomes a structured way to improve security, reduce risk, and build trust with customers and partners.
Turning Concern into Confidence
The most important takeaway from these conversations is this:
SMEs aren’t ignoring cyber security — they’re looking for clarity, simplicity, and reassurance.
Strong cyber resilience doesn’t require enterprise‑level complexity. It starts with:
- Understanding your real risks
- Fixing the basics well
- Having clear support when you need it
At Stiperstone, we work with Midlands SMEs to turn uncertainty into confidence — through practical IT support, cyber security guidance, and clear next steps that actually make sense for your business.
Not Sure Where Your Biggest Risks Are?
If any of the concerns above sound familiar, you’re not alone — and you don’t have to solve them on your own.
A short, no‑pressure IT & cyber health check can quickly highlight:
- Where your main risks sit today
- What needs attention now vs later
- How to strengthen your security without disrupting your business
👉 Get in touch to start the conversation.
01952 972 401
help@stiper.co.uk
Cyber Essentials - Security Advantage


Cyber Essentials - Security Advantage
Why Choosing a Cyber Essentials‑Certified MSP Gives Your Business a Real Security Advantage
When it comes to protecting your business, choosing the right Managed Service Provider (MSP) is one of the most important decisions you’ll make. But not all MSPs operate to the same security standard — and in a world of rising cyber threats, that difference matters.
Working with a Cyber Essentials‑certified MSP means choosing a partner who doesn’t just talk about security… they prove it.
Here’s why that matters for your organisation.
You’re Choosing a Provider With Verified Security Controls
Any MSP can claim to follow best practice — but Cyber Essentials requires them to demonstrate it.
Certification verifies that the MSP has strong controls in place across the five foundational areas of cybersecurity:
- Firewalls
- Secure configuration
- User access control
- Malware protection
- Secure and consistent patching
These verified safeguards reduce risk not only for the MSP, but for every client they support. A Cyber Essentials‑certified MSP is far less likely to be compromised — which means your business is far less likely to suffer a knock‑on supply‑chain attack.
It Shows They Take Security Seriously — Every Single Day
Cyber Essentials isn’t a passive badge. To stay certified, MSPs must maintain strong cyber hygiene across their entire organisation.
That means your MSP is committed to:
- Keeping systems properly configured
- Ensuring staff follow secure access practices
- Maintaining good patch management
- Reducing vulnerabilities across all customer environments
It’s a sign of discipline, accountability, and professional responsibility.
You Benefit From Stronger, More Secure Service Delivery
An MSP with Cyber Essentials baked into their processes works differently.
They bring:
- Standardised security baseline configurations
- More secure onboarding practices
- Better documentation and processes
- Reduced risk of human error
- Higher-quality, more resilient managed services
This leads to fewer vulnerabilities, fewer incidents, and fewer reactive support tickets — giving your business smoother, safer operations.
It Builds Trust Across Your Supply Chain
Your clients, partners, and suppliers increasingly expect businesses to demonstrate good cyber hygiene. Choosing a Cyber Essentials‑certified MSP strengthens your reputation by showing you’re taking cybersecurity seriously at every layer of your organisation — including your outsourced IT.
It demonstrates:
- You work with trusted, verified partners
- You value data security and continuity
- You minimise third‑party risk
- You’re reducing your overall threat exposure
This is especially important if you handle sensitive data, operate in a regulated sector, or bid for contracts where cybersecurity due‑diligence is mandatory.
It Helps Your Business Achieve Its Own Cyber Essentials Certification
If your organisation needs to obtain Cyber Essentials or Cyber Essentials Plus, choosing an MSP that already has certification makes the process significantly easier.
A certified MSP:
- Understands the requirements
- Already follows the controls
- Can help you align your systems
- Reduces remediation time
- Speeds up your path to certification
In other words: you’re not starting from zero — you’re building on a solid, compliant foundation.
You Get Real Cyber Protection — Not Just a Sales Pitch
Cyber Essentials‑certified MSPs operate with a proactive mindset. They don’t rely on guesswork or outdated practices — they follow a recognised, government‑backed standard designed to block the most common cyber threats.
This means your business benefits from:
- Reduced likelihood of malware infections
- Better defence against phishing and credential theft
- Stronger access controls
- Fewer misconfigurations
- More secure remote access and cloud environments
It’s practical, proven protection — day in, day out.
The Bottom Line
Choosing a Cyber Essentials‑certified MSP isn’t just a smarter choice — it’s a safer one.
You get a partner who meets recognised security standards, reduces your organisational risk, and strengthens your overall cyber resilience.
Ready to Work With a Cyber Essentials‑Certified MSP?
If you want greater security, stronger compliance, and a partner you can trust with your business‑critical systems, we’re here to help.
Get in touch today and discover how working with a Cyber Essentials‑certified MSP can transform your organisation’s security.
01952 972 401
help@stiper.co.uk
AI Driven Cyber Attacks
AI‑Driven Cyber Attacks
The New Frontier of Cyber Risk
As organisations accelerate digital transformation, a new category of threat is emerging — one that is faster, more adaptive and far harder to predict than anything before it. Artificial intelligence (AI) is no longer just a defensive asset. It has become a powerful weapon for cybercriminals, reshaping how attacks are launched and how quickly they spread.
In this article, we explore what AI‑driven cyber attacks are, why they’re becoming so dangerous, and how organisations can build resilience against this next wave of threats.
What Are AI‑Driven Cyber Attacks?
AI‑driven cyber attacks involve malicious actors using artificial intelligence — often in the form of autonomous or semi‑autonomous agents — to plan, execute and adapt attack campaigns with unprecedented speed.
Security researchers predict that by mid‑2026, at least one major global enterprise will fall victim to a breach significantly advanced by a fully autonomous AI system, capable of completing everything from reconnaissance to data exfiltration with minimal human involvement.
Unlike traditional malware, these AI systems can learn, evolve and respond dynamically to defences. This marks a shift from manually orchestrated intrusions to fast, self‑optimising attack chains.
Why AI‑Driven Attacks Are Becoming More Common
Multiple reports show the acceleration of AI‑powered cybercrime:
- AI‑driven cyberattacks surged by 87% in 2025, with one in six breaches involving AI‑enabled automation.
- 87% of organisations ranked AI‑related vulnerabilities as the fastest‑growing cyber risk heading into 2026.
- Attackers can now reverse‑engineer patches and deploy exploits before organisations even begin patching.
- AI‑assisted malware increasingly shifts behaviour mid‑attack to bypass detection.
Cybercriminals benefit from the same AI capabilities that defenders do: automation, speed, predictive analysis and the ability to process vast datasets instantly. But unlike defenders, attackers face no regulatory or ethical constraints.
How AI Is Transforming Cyber Attacks
- Autonomous Attack Cycles
Agentic AI systems can independently plan and execute complete attack lifecycles — from scanning attack surfaces to delivering payloads. These multi‑agent systems coordinate with one another, adjusting tactics in real time.
- Hyper‑Personalised Phishing
AI now analyses social media, emails, online behaviour and corporate news to craft messages tailored to individual targets — effectively eliminating the tell‑tale signs of traditional phishing.
This shift has already made phishing responsible for 91% of successful breaches.
Advanced deepfake tools further enhance social engineering effectiveness.
- Adaptive Malware
Modern AI‑enabled malware can rewrite its own code, generate new functions, or adjust behaviour mid-execution to evade detection — a major leap toward fully autonomous malware.
- Large‑Scale, Micro‑Targeted Attacks
The economics of cybercrime have flipped: what once required weeks of work and thousands in tooling now costs virtually nothing.
This shift enables highly targeted, “sniper‑level” attacks at the scale of mass campaigns.
- Long‑Term, Covert Intrusions
State‑linked groups already leverage AI to blend into normal network traffic and maintain long‑term access for months or years.
Why Traditional Cyber Security Tools Are Falling Behind
Classic defences — such as signature‑based detection and rule‑based monitoring — cannot keep up with malware that evolves in real time.
AI‑enabled threats operate at machine speed, while manual response processes remain measured in hours or days. This gap is widening rapidly. As one analysis highlights, attackers can now compromise systems far faster than organisations can trace or understand their movements.
The result: Defenders are outpaced not just in capability, but in time.
How Organisations Can Defend Against AI‑Driven Attacks
Although the threat landscape is evolving, several defence strategies have proven effective:
- AI‑Augmented Threat Detection
Defenders must use AI themselves — for behavioural analytics, anomaly detection, continuous monitoring and automated containment.
- Zero‑Trust Security Architecture
Zero Trust applied across models, data and infrastructure reduces the blast radius when AI‑powered intrusions occur.
- Rapid Recovery and Clean‑Environment Restoration
Resilience now depends on the ability to restore operations quickly.
Government security experts emphasise recovery as a primary strength indicator in the age of AI‑driven attacks.
- Continuous Red‑Teaming and AI‑Specific Testing
Defenders must regularly test against AI‑generated threats and simulated attack chains to stay ahead.
- Hardened Backups and Immutable Storage
Legacy backups are increasingly targeted. Threat hunting and validation of backup integrity is essential to avoid re‑infection during recovery.
The Future: A Race Between Offensive and Defensive AI
2026 marks a turning point. AI‑powered cyber threats are no longer experimental — they are active, autonomous and evolving fast. As attackers industrialise AI, defenders must adapt equally aggressively.
The organisations that thrive will be those that shift from reactive security to predictive resilience, treating AI not just as a tool, but as a foundational element of their security posture.
AI will remain both the greatest risk and the most powerful defence — and the race between the two has only just begun.
Ready to Strengthen Your Cyber Resilience?
AI‑driven attacks are evolving fast, and organisations can no longer rely on traditional defences. If you want to assess your current readiness, refine your cybersecurity strategy or explore practical steps to improve resilience, we’re here to help.
Get in touch today to book a consultation and ensure your organisation is prepared for the next generation of AI‑powered threats.
01952 972 401
help@stiper.co.uk
Cyber Security User Awareness Checklist
User Awareness Checklist for Cyber Security
Password Hygiene
- Use strong, unique passwords for every account.
- Enable Multi-Factor Authentication (MFA) wherever possible.
- Avoid sharing passwords; use a reputable password manager.
Software & System Updates
- Keep operating systems and applications up to date.
- Apply patches promptly to close vulnerabilities.
- Remove unused or outdated software.
Network Security
- Connect only to secure Wi-Fi networks.
- Use firewalls and antivirus tools.
- Avoid public Wi-Fi for sensitive tasks unless using a VPN.
Email & Phishing Awareness
- Verify sender details before clicking links or opening attachments.
- Report suspicious emails immediately.
- Never share sensitive information via email without encryption.
Device Security
- Lock your screen when away from your desk.
- Enable encryption on all devices.
- Keep endpoint protection active (e.g., Defender, EDR tools).
Data Protection
- Store sensitive data securely and encrypt it in transit.
- Apply least-privilege access controls.
- Back up critical data regularly.
Incident Response
- Know how to report a suspected breach or phishing attempt.
- Familiarise yourself with the organisation’s incident response plan.
- Participate in phishing simulations and awareness training.
Continuous Learning
- Complete scheduled e-learning modules on cyber security.
- Stay updated on new threats and compliance requirements.
- Engage in refresher training sessions regularly.
Final Thoughts
Cyber threats are evolving, and human error remains one of the biggest risks. Our latest blog, “User Awareness Checklist for Cyber Security”, outlines practical steps to strengthen your organisation’s defence—covering password hygiene, phishing awareness, device security, and safe browsing habits. Empower your team with knowledge to prevent costly breaches.
Want to improve your cyber resilience?.
Contact us today to discuss tailored security awareness training and managed solutions that keep your business safe.
01952 972 401
help@stiper.co.uk
Backup vs Disaster Recovery
Backup vs Disaster Recovery:
Why Your Business Needs Both to Stay Resilient
When it comes to protecting your business data, many organisations still confuse backup with disaster recovery. It’s an easy mistake to make—they both deal with data protection, right?
But here’s the truth: while they’re related, they serve very different purposes. And understanding the distinction is critical to building a resilient strategy that can withstand ransomware, hardware failure, and even human error.
Let’s break it down…
Backup: Your File-Level Safety Net
Backups are like a time machine for your files. Accidentally deleted a spreadsheet? Overwrote a critical document? Backups let you rewind and recover.
They’re designed to protect individual files and folders, making them ideal for day-to-day mishaps. But if your entire system goes down—say, due to a cyber attack or server failure—backups alone won’t get you back in business.
Disaster Recovery: Your Business Continuity Lifeline
Disaster recovery (DR) is about restoring operations, not just files. It’s the plan that gets your systems, applications, and infrastructure back online after a major disruption.
Think of it as your business’s emergency response system. DR ensures that even if your primary environment is compromised, you can switch to a secondary setup and keep things running.
Without a disaster recovery plan, your business could face hours, or even days, of downtime. And in today’s fast-paced world, that’s a risk few can afford.
Why You Need Both
At Stiperstone, we provide both backup and disaster recovery solutions. But the real value lies in knowing when and how to use each.
Backups are great for recovering lost or corrupted files.
Disaster recovery is essential for restoring full functionality after a major incident.
Together, they form a comprehensive resilience strategy that protects your business from:
- Ransomware attacks
- Hardware failures
- Human error
- Natural disasters
Real-World Example: Ransomware Strikes
Imagine this: your business is hit by ransomware. Files are encrypted, systems are locked, and operations grind to a halt.
With backups, you might be able to recover some files. But without a disaster recovery plan, your systems remain offline, your staff can’t work, and your customers are left waiting.
A combined strategy means you can restore files AND resume operations quickly, minimising disruption and protecting your reputation.
💬 Ask Yourself…
Do you know where your backups are stored?
Have you tested your disaster recovery plan recently?
Can your business survive a full day of downtime?
If you’re unsure about any of these, it’s time to take action.
We’re Here to Help
At Stiperstone, we specialise in helping businesses like yours build robust, tailored recovery plans. Whether you’re starting from scratch or refining an existing strategy, we’ll guide you through every step.
Because when the unexpected happens, you shouldn’t just recover—you should bounce back stronger.
Ready to strengthen your recovery plan? Let’s build resilience together.
Get in touch with us now and see how we can help!
01952 972 401
help@stiper.co.uk
MSP + AI = Success
Why Partnering with an MSP Makes AI Adoption
Easier, Safer, and Smarter
AI is transforming how businesses operate—but for small and medium-sized enterprises (SMEs), getting started can feel overwhelming. That’s where Managed Service Providers (MSPs) come in. They make AI adoption simple, secure, and scalable.
Here’s how...
Get Started Quickly with an MSP
Building an in-house AI team is a major undertaking. It requires recruiting skilled professionals, investing in training, and setting up the right infrastructure. For many small and mid-sized businesses, this simply isn’t feasible. That’s where Managed Service Providers (MSPs) come in. MSPs already have the expertise, tools, and experience to get your AI initiatives off the ground quickly. They understand the nuances of AI deployment and can tailor solutions to your specific needs. This means you can skip the lengthy setup and start seeing results faster.
Why it matters:
→ Skip the recruitment headaches and start seeing results sooner.
Use Top-Quality AI Tools Without the Hassle
MSPs often have established partnerships with leading technology providers like Microsoft, Google, and Amazon. These relationships give them access to powerful AI platforms and tools that might otherwise be out of reach for smaller businesses. The MSP handles everything—from licensing and setup to integration and maintenance—so you don’t have to worry about the technical details. You get the benefits of cutting-edge technology without the stress of managing it yourself.
Why it matters:
→ You get enterprise-grade tech—without the stress of managing licences or integrations.
Stay Safe and Follow the Rules
AI systems often process sensitive data, which means compliance with regulations like GDPR is critical. MSPs are well-versed in data protection laws and know how to build systems that are secure and compliant. They implement best practices for data handling, encryption, and access control, ensuring your business stays within legal boundaries. This not only protects your data but also shields your organisation from potential fines and reputational damage.
Why it matters:
→ Avoid fines and reputational damage with built-in security and compliance.
Ongoing Support and Improvements
AI isn’t a one-time project—it requires continuous monitoring, updates, and optimisation to remain effective. MSPs provide ongoing support to ensure your systems run smoothly and adapt to changing needs. They proactively manage performance, troubleshoot issues, and implement improvements, so your AI solutions stay sharp and relevant. This frees up your internal team to focus on strategic goals rather than technical upkeep.
Why it matters:
→ Focus on your business while experts keep your AI running smoothly.
Stay Ahead of the Competition
AI can give your business a significant edge—automating tasks, enhancing customer service, and uncovering new growth opportunities. MSPs help you identify where AI can deliver the most value and guide you through implementation. They ensure you’re not just keeping up with competitors, but staying ahead. With expert insights and strategic planning, MSPs help you leverage AI to innovate and grow.
Why it matters:
→ Gain a competitive edge in a fast-moving market.
Why Now Is the Time to Act
AI isn’t just for tech giants anymore. With the right MSP, SMEs can unlock powerful benefits—quickly and affordably.
Work Smarter, Not Harder
AI excels at automating repetitive tasks, allowing your team to focus on high-value work. Whether it’s data entry, scheduling, or customer queries, AI handles the routine so your staff can concentrate on strategy and innovation. This not only boosts productivity but also improves job satisfaction by reducing mundane workloads.
Why now? Time saved is money earned—and your team becomes more effective and engaged.
Make Better Decisions, Faster
AI transforms raw data into actionable insights. It helps you identify trends, predict outcomes, and make informed decisions with confidence. From sales forecasting to customer behaviour analysis, AI provides clarity and speed, enabling you to respond quickly to market changes and opportunities.
Why now? In a fast-paced environment, timely and accurate decisions are key to success.
Boost Customer Experience
AI-powered tools like chatbots and recommendation engines enhance customer interactions. They provide instant support, personalised experiences, and 24/7 availability. This leads to higher satisfaction, increased loyalty, and better retention rates. Customers expect fast and relevant service—and AI helps you deliver it.
Why now? Happy customers are loyal customers—and AI helps you keep them engaged.
Cut Costs Without Cutting Corners
AI improves operational efficiency by reducing errors, streamlining workflows, and optimising resource use. You can achieve more with less—without compromising on quality. This is especially valuable in tight economic conditions, where cost control is essential for sustainability.
Why now? Leaner operations mean stronger margins and better scalability.
Stay Ahead of the Curve
AI is no longer a futuristic concept—it’s a present-day necessity. Businesses that adopt AI early are already seeing the benefits in innovation, efficiency, and growth. MSPs make it easier to take that leap, providing the guidance and support needed to integrate AI successfully. Don’t wait until it’s too late—start now and lead the way.
Why now? The future is here. Don’t get left behind.
Ready to explore AI for your business?
Let’s talk about how Stiperstone can help you get started – with the right MSP, the right tools, and the right strategy.
Get in touch with us now and see how we can help!
01952 972 401
help@stiper.co.uk
Cyber Hygiene
Cyber Hygiene: The Everyday Essentials for Digital Resilience
In recent years, cyber threats are becoming more sophisticated, but the foundations of good cyber security remain surprisingly simple. Cyber hygiene refers to the routine practices and behaviours that help individuals and organisations maintain the health and security of their digital environments.
At Stiperstone, we believe that strong cyber hygiene is not just a checklist—it’s a mindset. And with the support of AI technologies, maintaining that mindset has never been more achievable.
Understanding Cyber Hygiene
Cyber hygiene is much like personal hygiene. It involves regular, proactive habits that prevent problems before they arise. These habits form the first line of defence against cyber incidents, from phishing attacks to ransomware.
Key elements include:
- Using strong, unique passwords
- Keeping software and systems up to date
- Backing up data securely
- Training staff to recognise threats
- Monitoring for unusual activity
These practices may seem basic, but they are often the difference between a minor inconvenience and a major breach.
How AI Enhances Cyber Hygiene
Artificial Intelligence is transforming the way we approach cyber security. As your Managed Service Provider, we integrate AI tools to make cyber hygiene smarter, faster, and more effective.
Here’s how:
1. Intelligent Threat Detection
AI continuously monitors systems for suspicious behaviour, identifying threats before they escalate. This allows for faster response times and reduces reliance on manual oversight.
2. Automated Updates and Patching
Keeping software up to date is critical. AI can automate patch management, ensuring vulnerabilities are addressed promptly without disrupting operations.
3. Behavioural Analysis
AI tools learn typical user behaviour and flag anomalies—such as unusual login times or access patterns—that may indicate a breach.
4. Enhanced Training and Awareness
AI-driven simulations and adaptive training platforms help staff stay alert to evolving threats, tailoring content to individual learning needs.
Building a Culture of Security
Good cyber hygiene isn’t just about technology, it’s about people. We help organisations embed security into their culture, empowering teams with the tools and knowledge they need to stay safe.
This includes:
- Regular awareness training
- Clear policies and procedures
- Support for secure remote working
- Ongoing guidance from our expert team
What does good Cyber Hygiene look like?
🔐 Password Management
- Use strong, unique passwords for each account
- Enable multi-factor authentication (MFA)
- Use a reputable password manager
🧼 System and Software Maintenance
- Keep operating systems and software up to date
- Regularly patch vulnerabilities
- Remove unused or outdated applications
🛡️ Network Security
- Use firewalls and antivirus software
- Secure Wi-Fi networks with strong encryption
- Segment networks to limit access
📚 User Awareness and Training
- Conduct regular cyber security awareness training
- Educate staff on phishing and social engineering tactics
- Promote a culture of security-first thinking
📁 Data Protection
- Encrypt sensitive data at rest and in transit
- Implement access controls and permissions
- Back up data regularly and securely
🔍 Monitoring and Response
- Monitor systems for unusual activity
- Set up alerts for potential threats
- Have an incident response plan in place
🤖 AI and Automation Support
- Use AI tools to detect and respond to threats faster
- Automate routine security tasks like patching and monitoring
- Analyse user behaviour to identify anomalies
Final Thoughts
Cyber hygiene is not a one-time effort—it’s an ongoing commitment. With AI as your ally and Stiperstone as your partner, you can turn best practices into everyday behaviours that protect your business from the inside out.
Let’s talk about how we can help you build a resilient, security-first organisation.
Get in touch with us now and see how we can help!
01952 972 401
help@stiper.co.uk
Copilot: Top 5 Uses in Microsoft Teams


Copilot in Microsoft Teams: Top 5 Uses (with Prompts)
Artificial intelligence is the current headline technology of the 2020s. With so many ways for organisations to use AI, making sure that you’re up to date with the latest advancements in AI will ensure that you have an edge against the competition.
Microsoft’s sensational AI productivity tool — Microsoft 365 Copilot — is shaping the way organisations do things. With so many functionalities and tools available with just a simple prompt, it’s making workflows far more efficient while also providing a host of new knowledge and power to the workplace.
As Copilot is integrated into all of the Microsoft 365 applications, in this article, we’ll be going over the top 5 use cases for Copilot within Microsoft Teams, to ensure that you can make the most of your organisation’s communications and collaboration capabilities by empowering them with AI.
Top Copilot in Microsoft Teams Uses
Summarise Meeting Notes
Microsoft Teams is the epicentre of the workplace meeting. These meetings are vital — but, the only way you can take advantage of the meeting is by taking what was said in the meeting and applying it. This is why notes are so handy, as they let you turn what is essentially a discussion into an actionable list.
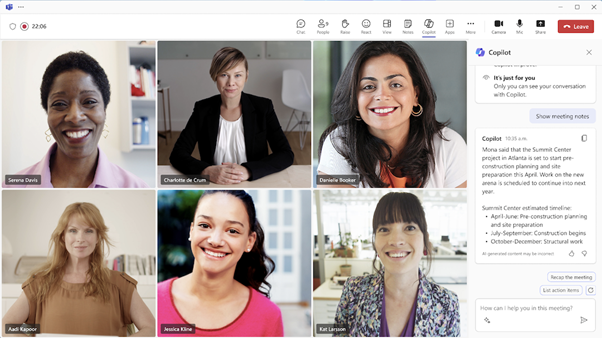
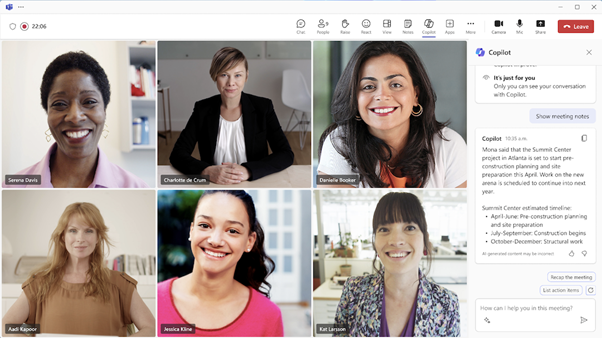
However, taking meeting notes can be a pain. Keeping up with everything that’s been said is difficult, and you might miss key details or even just have notes that are messy and aren’t clear.
Microsoft Copilot lets you turn your Microsoft Teams meeting into a bunch of summarised notes with just a simple prompt. All you have to do is ask — either during the meeting or afterwards in the recap screen — with a simple prompt such as ‘Summarise the meeting in simple notes’, and Copilot will do the rest.
You can also further this by customising your prompts to better suit your needs. For example, if you want to summarise the meeting and create a list of locations mentioned, you can ask Copilot to do so and it will.
Catch-up when Attending Late
Sometimes, being late can be unavoidable. Even the most organised people sometimes get hit by delays, clashes, or even traffic. Microsoft Copilot will easily ensure that you’re able to catch up with what you’ve missed, by summarising it for you so you can ensure that you’re in the loop as you go forward.
All you have to do is ask Copilot to ‘summarise the meeting so far, with all the key points’ and it will do so, giving you everything that you need to be involved in the conversation. You can also use Copilot’s meeting recap capabilities afterwards to go over everything that you’ve missed, making sure that you’re clear about everything that was discussed.
Using Chat to Create Agendas
As much as post-meeting actions are important, ensuring that your meeting is productive and successful is also vital. This is done by using an agenda — and Microsoft Copilot helps you make agendas faster than ever.
All you need to do is ask Copilot to make an agenda for a meeting — such as ‘make an agenda for my meeting with Claire about business operations’ — and it’ll use your organisational data to make an effective agenda.
You can then chat with Copilot to adjust this however you need — simply just talk to your Copilot to tell them exactly what you want from your agenda, to make sure it’s perfect. By doing so, you can create a much better and more in-depth agenda far more quickly than having to do it yourself.
Capture and Assign Actions
As mentioned previously, you can use Copilot to summarise meeting notes and ensure that the post-meeting actions are clear. However, you can also use Copilot to capture exactly who is meant to do what action — and have it presented.
By doing so, everyone is clear about what they need to be doing, meaning the meeting will have been more productive and effective — and all it takes is a simple prompt.
All you need to do is ask Copilot to ‘summarise everyone’s post-meeting actions’ and it will do so, meaning that you can have a clear list of who is meant to do what without having to remember back or relying on notes — and preventing responsibilities from getting tangled.
Catch-up on Messages After Leave
When you’re on company leave, you miss a lot of information. And while you can use your emails and memos to get a good idea of what you’ve missed, you simply miss a lot of the day-to-day conversations. However, going back through missed Teams messages can just take time and be confusing.
Copilot helps with this immensely. You can simply ask Copilot to ‘summarise everything I’ve missed in the R&D chat since I went on vacation’ and Copilot will do the rest — giving you a summary of everything that’s happened since you went away.
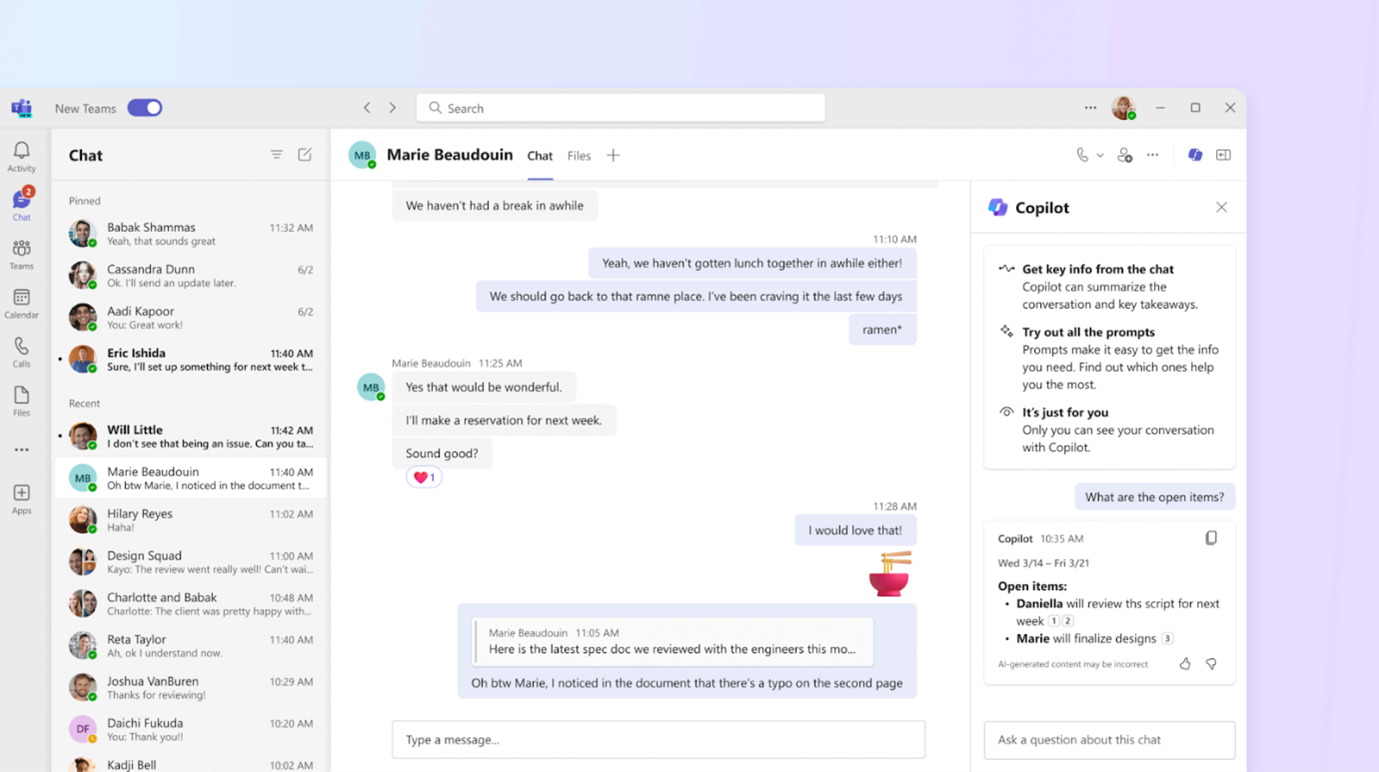
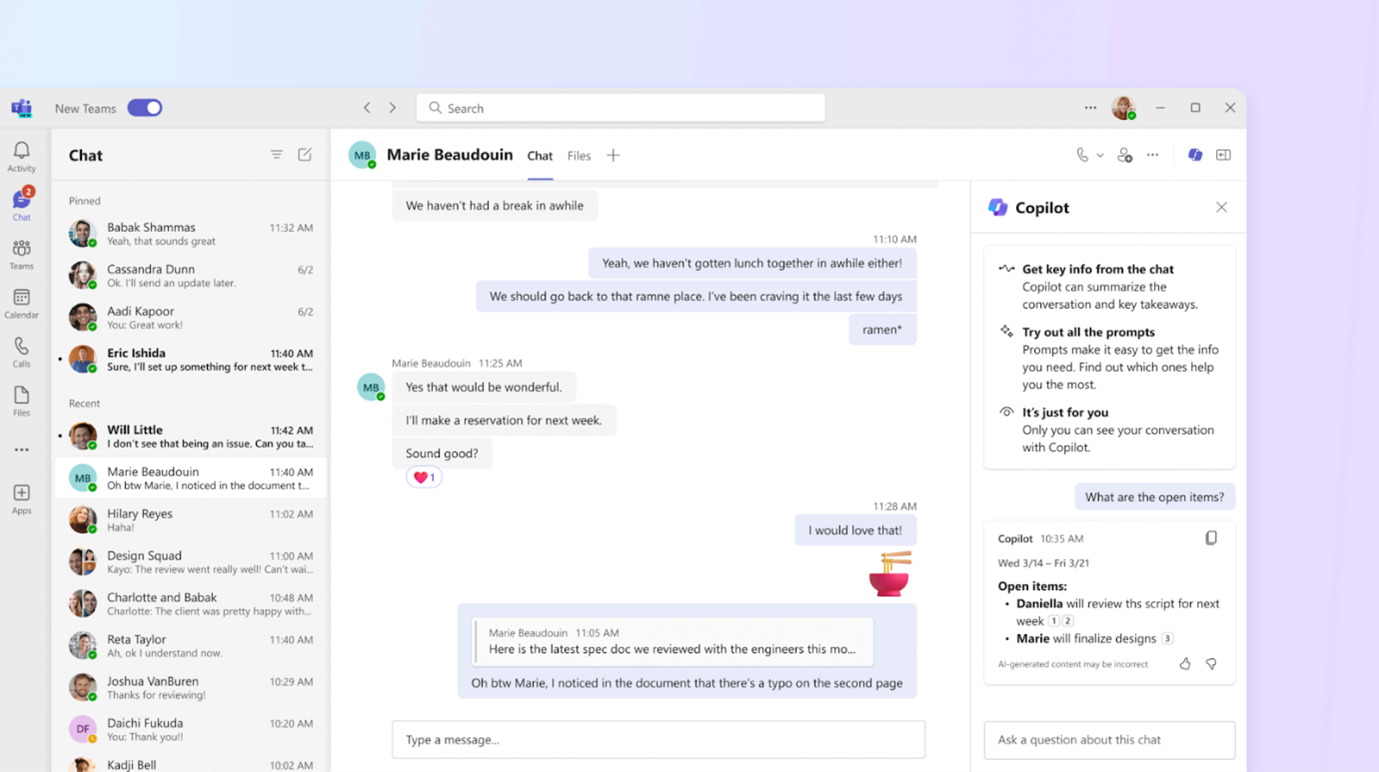
However, going further than this, you can also ask Copilot if certain things have been discussed or addressed in that time. Simply just ask a question, such as ‘has the R&D team developed the second prototype name since I went on vacation?’ and Copilot will be able to use its organisational data to be able to work out the answer.
How to Get Started
Microsoft 365 Copilot is a strong piece of technology that truly enriches Microsoft Teams, and lets you take the capabilities of the premier communications software to the next level. Using Copilot, you can easily shorten tasks that would take hours, and make sure that you’re in the loop at all times, no matter what.
If you’re looking to take advantage of Copilot but don’t know where to start, reach out to us today. Our experts are here to help you get started, and will make sure that Copilot is set up properly within your organisation — while also answering any questions you may have.
Get in touch with us now and see how we can help!
01952 972 401
help@stiper.co.uk
AI and Social Engineering: A Double-Edged Sword in Cyber Security
AI and Social Engineering: A Double-Edged Sword in Cybersecurity
In today’s digital landscape, social engineering remains one of the most potent tools in a cyber criminal’s arsenal. But with the rise of artificial intelligence (AI), the threat—and the defence—has evolved dramatically. This blog explores how AI is reshaping social engineering, drawing on insights from recent training materials and the latest cybersecurity intelligence.
Understanding Social Engineering
At its core, social engineering is the art of manipulating people into revealing confidential information or performing actions that compromise security: attackers exploit human psychology—trust, urgency, fear of missing out—to trick individuals into clicking malicious links, sharing credentials, or transferring funds.
Common tactics include:
- Phishing: Mass emails or texts designed to lure victims into clicking malicious links.
- Spear Phishing and Whaling: Targeted attacks on individuals or executives.
- Business Email Compromise (BEC): Impersonation of trusted contacts to request fraudulent payments or sensitive data.
These attacks often bypass technical defences by exploiting the “human loophole.”
AI as an Enabler of Social Engineering Attacks
AI has supercharged traditional social engineering in several alarming ways:
1. Hyper-Realistic Phishing
Generative AI tools can now craft phishing emails that are grammatically perfect, contextually relevant, and visually indistinguishable from legitimate communications. Attackers use AI to mimic tone, branding, and even writing styles.
2. Deepfake Voice and Video
Voice cloning and deepfake video technologies allow attackers to impersonate executives or colleagues in real-time, issuing fraudulent instructions via phone or video calls. This has led to a surge in voice phishing (vishing) attacks, where cloned voices are used to pressure employees into urgent actions like transferring funds or revealing credentials.
3. Automated Reconnaissance
AI can scrape social media and public data to build detailed profiles of targets, enabling highly personalised spear phishing campaigns.
4. Thread Hijacking at Scale
Attackers can use compromised inboxes to hijack email threads – AI can automate this process, scanning for keywords like “Re:” and crafting believable replies laced with malware.
Emerging Trends in AI-Driven Social Engineering (2025 Update)
Deepfake Detection Becomes Critical
With deepfakes now a common tool in social engineering, organisations are investing in detection tools and analogue verification protocols—such as confirming requests via known phone numbers or in person—to counteract this threat.
AI Governance and Policy Enforcement
As AI tools become embedded in daily operations, organisations must implement governance frameworks. This includes:
- Clear policies on AI use and data handling
- Regular audits of AI-generated content
- Training staff to recognise AI-generated threats
Leadership must embed these practices into organisational culture to ensure resilience.
Ransomware-as-a-Service (RaaS) and AI
Ransomware groups are using AI to identify high-value targets and optimise attack timing. AI also helps craft persuasive ransom notes and automate malware distribution, making patch management and incident response planning more critical than ever.
Insider Threats and AI Misuse
AI tools can be misused by insiders—either maliciously or unintentionally. For example, an employee might use a generative AI tool to summarise sensitive internal documents, inadvertently exposing confidential data. Organisations are now monitoring internal AI usage and applying data loss prevention (DLP) tools to mitigate this risk.
Defending Against AI-Enhanced Social Engineering
Fortunately, AI is also a powerful ally in defence. Here are key strategies organisations are adopting in 2025:
1. AI-Powered Detection
Defensive AI tools can analyse communication patterns, detect anomalies, and flag suspicious behaviour in real time—often before a human would notice.
2. Zero Trust Architecture
Implementing zero trust principles—where no user or device is automatically trusted—helps limit the damage from compromised accounts.
3. Multi-Factor Authentication (MFA)
MFA remains a cornerstone of defence, making it harder for attackers to exploit stolen credentials.
4. Enhanced Awareness Training
Training must evolve to teach employees how to spot AI-generated content, including deepfakes and hyper-realistic phishing. Awareness is no longer about spotting typos—it’s about questioning even the most convincing messages.
5. Monitoring and Governance of AI Systems
Organisations must inventory and monitor their own AI tools to prevent misuse or compromise, including guarding against data poisoning and prompt injection attacks.
Conclusion: Stay Sceptical, Stay Secure
The goal isn’t to memorise every attack type—it’s to cultivate a mindset of healthy scepticism. Social engineering thrives on trust. In an AI-powered world, that trust must be earned, verified, and never assumed.
Whether at work or in your personal life, vigilance is your best defence.
Get in touch:
01952 972 401
help@stiper.co.uk
Cyber Attacks on Retail Giants
The Hidden Threat: Understanding and Preventing Cyber Security Supply Chain Attacks
In an increasingly interconnected digital world, the strength of your cyber security is only as robust as the weakest link in your supply chain. Recent events have once again brought this reality into sharp focus—most notably, the cyber attacks on UK retail giant Marks & Spencer and global sportswear brand Adidas.
The M&S and Adidas Breaches: Costly Lessons in Supply Chain Risk
According to the Financial Times, Marks & Spencer attributed its breach to a supplier vulnerability, which is expected to cost the company approximately £300 million in operating profit for the 2025/26 financial year.
Just weeks later, Adidas disclosed that a third-party customer service provider had been breached, exposing customer data from individuals who contacted Adidas support centres in Turkey and South Korea in 2024 or earlier.
The compromised data included names, email addresses, phone numbers, and the content of customer service messages.
These incidents underscore a critical truth: even the most sophisticated internal defences can be bypassed if third-party partners are not held to the same security standards.
What Are Supply Chain Attacks?
Supply chain attacks occur when cybercriminals infiltrate an organisation by targeting its suppliers, vendors, or service providers. These attacks exploit the trust and access granted to third parties, allowing malicious actors to bypass perimeter defences and gain entry to sensitive systems.
As outlined in a recent article by SentinelOne, these attacks can be software-based—injecting malicious code into updates or libraries—or hardware-based, compromising devices during manufacturing. The infamous SolarWinds breach is a textbook example, where attackers inserted a backdoor into a software update, affecting thousands of organisations globally.
Why Do Supply Chain Attacks Happen?
Several factors make supply chains attractive targets:
- Weak Security Controls: Many vendors lack robust cyber defences, making them easier to compromise.
- Lack of Visibility: Organisations often have limited insight into their suppliers’ security postures.
- Complexity and Scale: The more vendors you work with, the larger your attack surface becomes.
- Trust Exploitation: Once inside, attackers can move laterally across networks, often undetected.
A recent article from Calcalist Tech highlights how attackers are increasingly targeting the “soft underbelly” of organisations—third-party providers who may not be subject to the same rigorous security protocols. In fact, 62% of network intrusions now originate from third-party sources, with financial impacts exceeding those of direct breaches due to reputational damage and business disruption.
What Can Be Done?
Mitigating supply chain risk requires a multi-layered approach:
- Vendor Risk Assessments: Regularly evaluate the security posture of all third-party partners.
- Zero Trust Architecture: Never assume trust—verify every user, device, and connection.
- Continuous Monitoring: Use tools that provide real-time visibility into third-party activity.
- Contractual Security Clauses: Ensure vendors are contractually obligated to meet specific security standards.
- Incident Response Planning: Include third-party breach scenarios in your response playbooks.
Assess Your Risks Now
At Stiperstone, we’ve seen first hand how devastating supply chain attacks can be—not just in terms of financial loss, but in eroding customer trust and operational resilience.
If you’re unsure about the security of your own supply chain, don’t wait for a breach to find out. Contact Stiperstone today for expert guidance on securing your digital ecosystem. Our team can help you assess your current risks, implement best practices, and build a resilient supply chain that supports—not threatens—your business goals.